Null sender address
A question came up on the email geeks slack channel about empty from addresses. I asked if they meant the 5321 or 5322 from address which prompted a question about if you could even have a null 5321 from.
Yes, you can and it’s commonly used for some types of email.
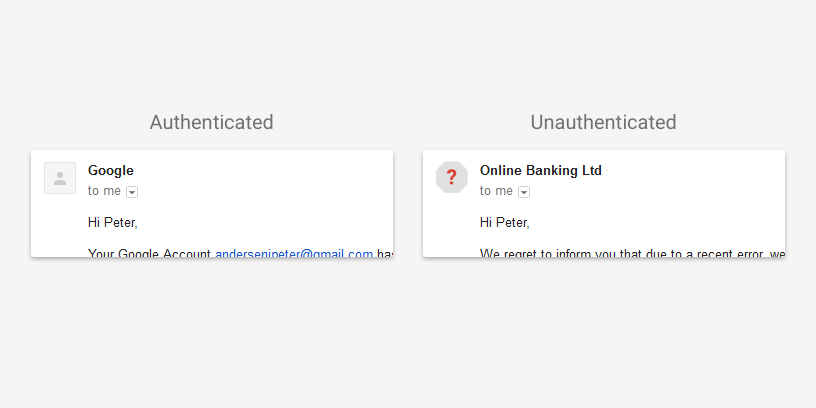
5321.from is the bounce address, and the domain used in SPF authentication. Null addresses, literally <>, are used for email where it’s not important to know if it wasn’t delivered. If the mail fails to deliver it usually is just dropped on the floor and no one ever knows anything.
If the 5321.from is the SPF domain and there is an entire class of email that doesn’t have a 5321.from, what do we do about SPF? Never fear, the SPF spec addresses that. When the message has a null from address, the domain in the HELO is checked for a SPF record.