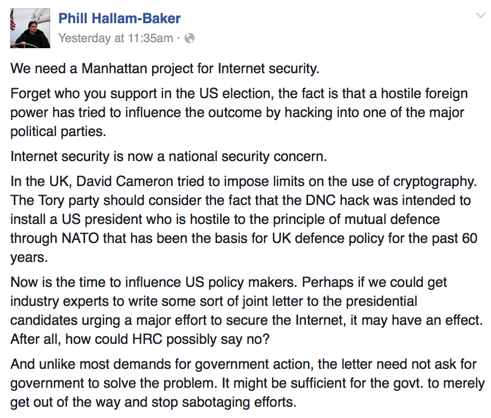
Google accounts breached
Over 1 million Google accounts breached by Android malware.
There are some folks I know who really can’t understand why I stick with Apple over Android. The above issue is a big one. Doing what we do, security is a major consideration. I don’t need my accounts, or other accounts I have access to, compromised. It’s not that Apple is 100% compromise proof, but there are more checks and balances in the pipeline.
On the deliverability front, I had a recent interaction with someone from iCloud. This is a colleague I’ve worked with for years now, following him through multiple job changes. A client was having some delivery issues with a shared IP, so I was asking if he could send me some data to help track down the problem customer. I have a habit of asking for subject lines when I’m trying to get data. It’s usually enough for an ESP to track down the problem, and they’re not a way for folks to track down spamtraps or recipients. The answer I got back was sorry, they couldn’t give me any information at all, even something minor like a subject line.
Apple takes user privacy seriously and are doing a lot to protect their users. Does that mean I spend too much money on hardware I could buy cheaper? Perhaps. But, I’ll pay a little more to work with a company that puts privacy at the center of their product suite.