Security issues affect us all
I’ve been talking about security more on the blog. A lot of that is because the security issues are directly affecting many senders. The biggest effect recently has been on companies ending up on the SBL because their signup forms were the target of a subscription attack. But there are other things affecting online spaces that are security related. Right now not much of it is affecting email senders, but it’s good to be aware of.
DDOS attacks
There has been an increase in DDOS attacks against different companies and network. Some of the online game sites have been targeted including EA, Blizzard and others. A group called PoodleCorp is claiming responsibility for those attacks.
Another set of DDOS attacks hit Brian Krebs’ website this week. The site stayed up, but Akamai has told Brian they can no longer host his website. His website is down for now and the foreseeable future.
While this activity doesn’t affect marketers directly, it does tell us that there is active development happening on the less legal side of the internet. The volumes of the recent attacks have sent records. They’re also changing in scope and including new kinds of traffic in an effort to knock sites offline. Even more concerning, they appear to be systematically attempting to discover defenses in order to attack the internet as a whole.
Increase in Spam
Spam has been on the decrease over the last few years. Many of us were treating it as a mostly-solved problem. But a new report from Cisco Talos shows that trend is reversing and spam levels are increasing. Current levels are approaching those last seen more than 5 years ago. Cisco Talos has used a number of different sources of data, all showing an increase in spam directly and indirectly.
CBL Volumes over past 10 years:
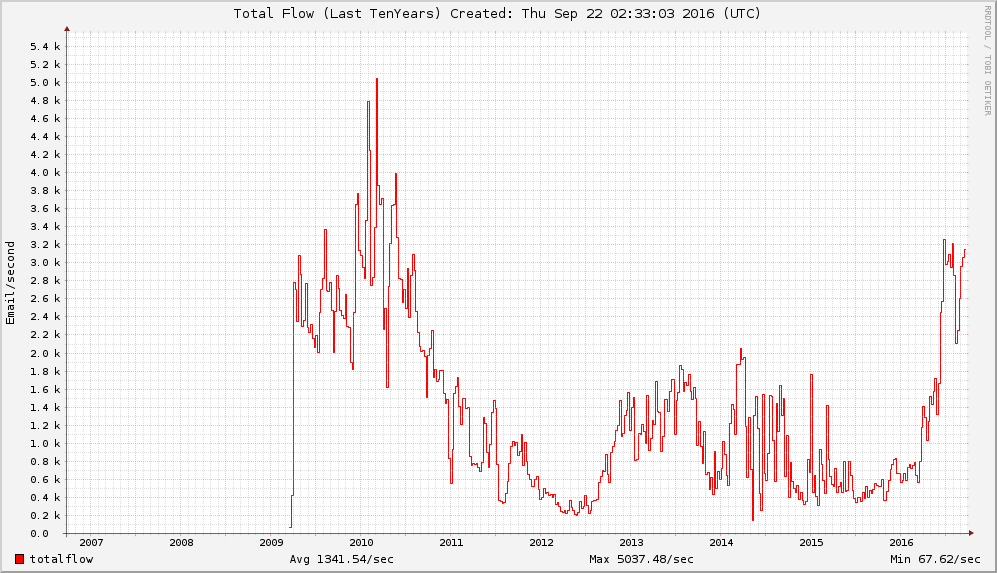
Cisco Talos also looks at the number of IP addresses in the Spamcop blocklist as a proxy for the amount of spam sent. Average numbers of listed IPs have doubled over pre-2106 levels.
According to the author, this rise is mostly attributed to the Necurs botnet. This botnet is a little different than most, in that it only uses a small subset of infected machines for each spam run. It sends some mail, and then the bot goes quiet.
While this doesn’t affect marketers directly, it does mean that spam filters will be under even more active development. I’ve actually seen some of this increase in activity myself. For me, the addresses hit hardest are the ones stolen from ESPs and retailers over the years.
ISPs being compromised
This week Yahoo announced that over 500 million accounts were compromised. Account owners are being alerted to update their passwords when they log in. Yahoo also cautions that actual Yahoo mail will have a special badge when viewed in the Yahoo web client and the smartphone applications.
The icon is a small purple Y next to the from address in the inbox:![]()
And in the message itself: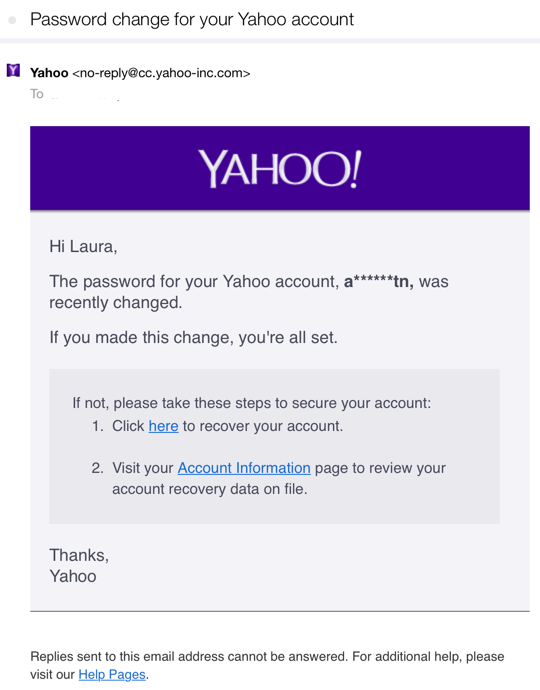
Of concern is that Yahoo has attributed the hack to state sponsored actors. On the surface it’s hard to believe that a government would care about getting into people’s Yahoo mail. But, as Yahoo and other mail providers are used worldwide, they may be looking for access to certain accounts and it’s easier to take all of them or some of them. Yahoo has set up a website for customers concerned about the compromise and to answer common questions.
For marketers this isn’t necessarily a direct concern. However, companies that tie account access to email addresses need to address the security of those accounts. What happens when the email address is compromised? How easy is it for someone to get into your system if they own someone else’s email address? Can they find credit card numbers and other PII?
What next?
Well, we don’t really have a what’s next. But security is a major issue online and with the active development of new tools everyone online needs to start prioritizing security. What are your defenses? What happens when you’re compromised? What can you do? Who do you call? These discussions need to happen and they need to happen sooner or later.
