Finally! Spam has a purpose
 Author Julie Czerneda posted about some of her writing techniques on Jim C. Hines’ blog today. Julie is one of my favorite authors. She’s a biologist so her science writing flows well for me. Too many folks try to write biology and get little nitpicky details wrong and it can disrupt the whole book for me. I spend way too much time thinking about the actual biology and lose track of the plot.
Author Julie Czerneda posted about some of her writing techniques on Jim C. Hines’ blog today. Julie is one of my favorite authors. She’s a biologist so her science writing flows well for me. Too many folks try to write biology and get little nitpicky details wrong and it can disrupt the whole book for me. I spend way too much time thinking about the actual biology and lose track of the plot.
One part of her post stood out and made me smile, though.
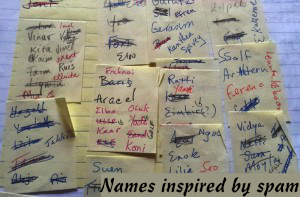
[…] my inbox kept getting spammed. Rather than let myself get annoyed, I’d jot down the more interesting names before deleting. Soon I had the collection shown in small part here. To my joy—and perhaps with a smidge of righteous vengeance—my spammers proved perfect names for many of the Om’ray, and others.
Spam is useful for something!
The whole blog post is worth a read, though. I am doing more and more writing these days, albeit not fiction, and hearing how actual authors write has helped me both write better and spend less time staring at the screen wondering what to say next.